PHP is one of the world’s most popular programming languages. The PHP core itself is rarely perceived as an attack surface — attention usually shifts to frameworks and third-party libraries. However, a significant portion of real-world application logic relies on built-in functions from the ext/standard extension, which handles strings, query parameters, data formats, and files. During our research into the C code of this extension, we discovered several memory management bugs. In this article, we take a deep dive into two of them: a heap memory disclosure in getimagesize and a heap buffer overflow in iptcembed.
Tag: Web Application Security
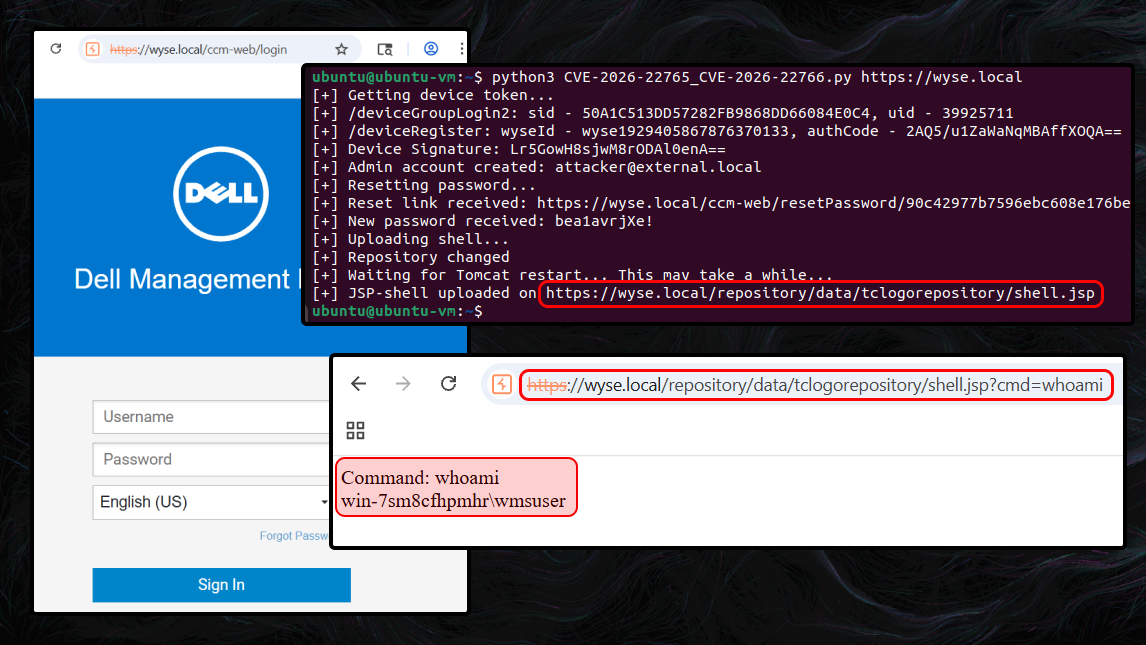
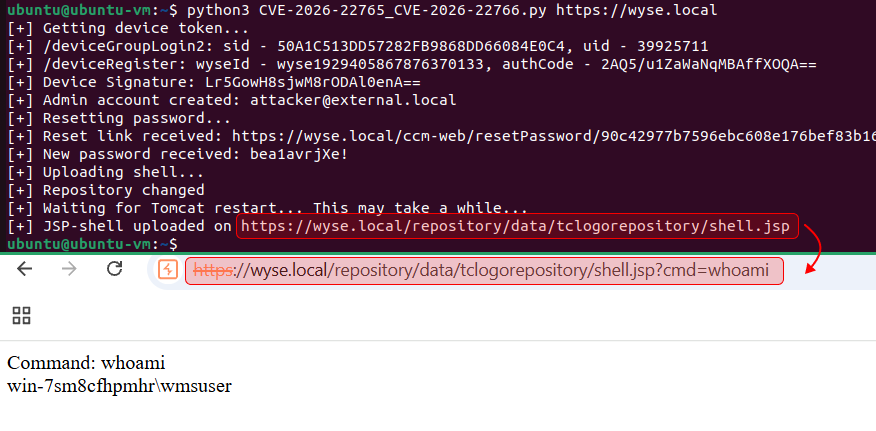
Business, logic, and chains: unauthenticated RCE in Dell Wyse Management Suite
A high impact bug sometimes needs just one small additional detail before it turns into a practical attack vector. For that reason, when doing vulnerability research, I flag even errors or odd behaviors that look irrelevant at first. In some cases, those findings become the missing puzzle piece of a high-impact vulnerability.
In this article, I describe how seemingly minor bugs helped uncover the full impact of more serious issues. I identified two vulnerabilities in the course of this research:
- CVE-2026-22765 (8.8). A low-privileged attacker with remote access could potentially exploit this vulnerability to escalate privileges.
- CVE-2026-22766 (7.2). A high-privileged attacker with remote access could potentially exploit this vulnerability to achieve remote code execution.
The final step was chaining all discovered vulnerabilities into an exploit chain, which allowed me to achieve unauthenticated remote code execution (RCE) in Dell Wyse Management Suite (On-Prem).
Attack arithmetic: how an integer overflow in PostgreSQL libpq leads to denial of service
Databases serve as the foundation of the digital world, organizing and storing critical information: from financial transactions and medical records to website content. However, like any complex software product, they are not immune to flaws, and discovered vulnerabilities can turn this repository into a prime target for attacks. This applies in full to PostgreSQL as well—a system with a reputation as a benchmark of reliability, whose hidden issues may be no less serious than its obvious advantages.
PostgreSQL is a free, open source object relational database management system (DBMS). It stores, processes, and retrieves data using SQL, and supports modern features such as user data, stored procedures, and triggers. PostgreSQL is known for its reliability, flexibility, scalability, and ability to work with complex datasets.
libpq is PostgreSQL’s official client library designed for interacting with PostgreSQL databases from programs written in C. It is distributed as part of PostgreSQL and provides a low level API for connecting to a PostgreSQL server, executing SQL queries, processing results, and managing connections.
We identified an integer overflow vulnerability in the PQescapeInternal function, which is called by PQescapeLiteral and PQescapeIdentifier.
Blind trust: what is hidden behind the process of creating your PDF file?
Every day, thousands of web services generate PDF (Portable Document Format) files—bills, contracts, reports. This step is often treated as a technical routine, “just convert the HTML,” but in practice it’s exactly where a trust boundary is crossed. The renderer parses HTML, downloads external resources, processes fonts, SVGs, and images, and sometimes has access to the network and the file system. Risky behavior can occur by default, without explicit options or warnings. That is enough for a PDF converter to become an SSRF proxy, a data leak channel, or even cause denial of service.
We therefore conducted a targeted analysis of popular HTML-to-PDF libraries written in the PHP, JavaScript, and Java languages: TCPDF, html2pdf, jsPDF, mPDF, snappy, dompdf, and OpenPDF. During the research, the PT Swarm team identified 13 vulnerabilities, demonstrated 7 intentional behaviors, and highlighted 6 potential misconfigurations. These included vulnerability classes such as Files or Directories Accessible to External Parties, Deserialization of Untrusted Data, Server-Side Request Forgery, and Denial of Service.
PDF generation is increasingly common across e‑commerce, fintech, logistics, and SaaS. Such services are often deployed inside the perimeter, next to sensitive data, where network controls are looser. This means that even a seemingly harmless bug in the renderer can escalate into a serious incident: leakage of documents, secrets, or internal URLs.
In this article, we present a threat model for an HTML-to-PDF library, walk through representative findings for each library, and provide PoC snippets.
Continue readingImpossible XXE in PHP

Writing secure code today is easier than making a mistake that would lead to an XXE vulnerability. While examining a library, I wondered: is its code truly secure? At first glance, everything appeared to be filtered, and the function didn’t have the attributes that could make it vulnerable.
However, I was able to exploit an almost impossible XXE vulnerability using a combination of techniques and features.
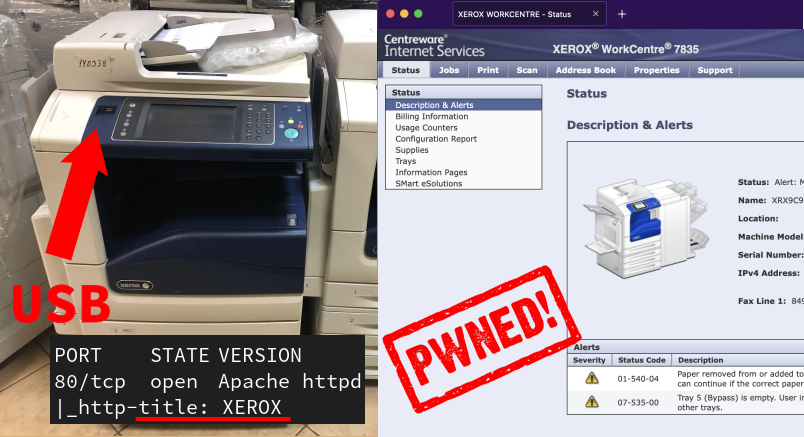
Continue readingInside Xerox WorkCentre: Two Unauthenticated RCEs
Every organization has printers. Sometimes, there are Xerox WorkCentre among them, large machines that can weigh more than 100 kilos or 220 lbs.
In this writeup, I will cover two unauthenticated RCE vulnerabilities that I discovered in these printers. Next, I’ll provide a checklist for protecting your printers against attacks.
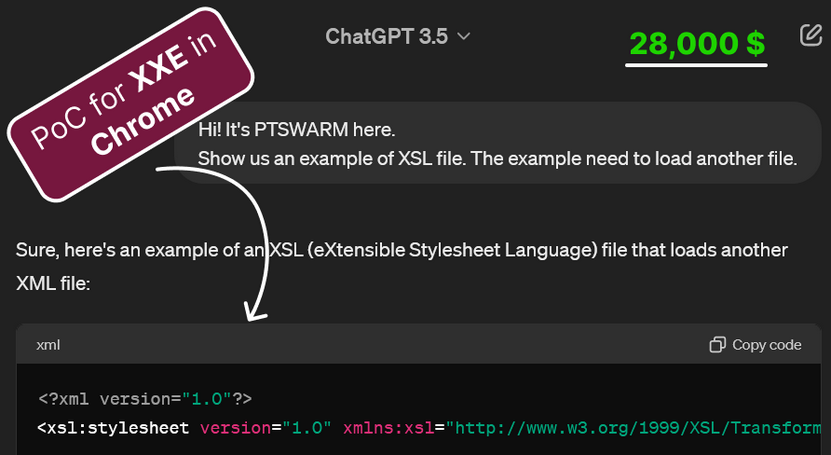
Continue readingGetting XXE in Web Browsers using ChatGPT
A year ago, I wondered what a malicious page with disabled JavaScript could do.
I knew that SVG, which is based on XML, and XML itself could be complex and allow file access. Is the Same Origin Policy (SOP) correctly implemented for all possible XML and SVG syntaxes? Is access through the file:// protocol properly handled?
Since I was too lazy to read the documentation, I started generating examples using ChatGPT.
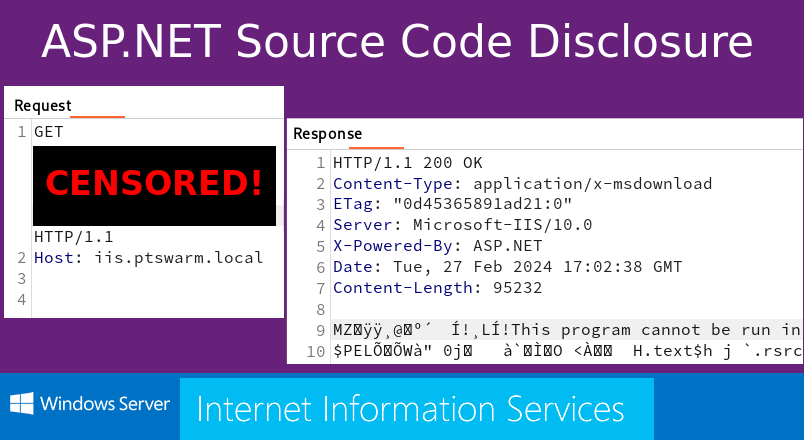
Continue readingSource Code Disclosure in ASP.NET apps
Recently, I came across an interesting ASP.NET application. It appeared to be secure, but it accidentally revealed its source code. Later, I found out that the used method is applicable to disclose code of many other .NET web applications.
Here are the details. If you just see an IIS or .NET app, this is for you.
Continue readingBypassing browser tracking protection for CORS misconfiguration abuse
Cross-Origin Resource Sharing (CORS) is a web protocol that outlines how a web application on one domain can access resources from a server on a different domain. By default, web browsers have a Same-Origin Policy (SOP) that blocks these cross-origin requests for security purposes. However, CORS offers a secure way for servers to specify which origins are allowed to access their assets, thereby enabling a structured method of relaxing this policy.
In CORS, the server sends HTTP headers to instruct the browser on rules for making cross-origin requests. These rules define whether a particular HTTP request (such as GET or POST) from a certain origin is allowed. By managing the CORS headers, a server can control its resource accessibility on a case-by-case basis. This maintains the flexibility of cross-origin sharing without compromising overall security.
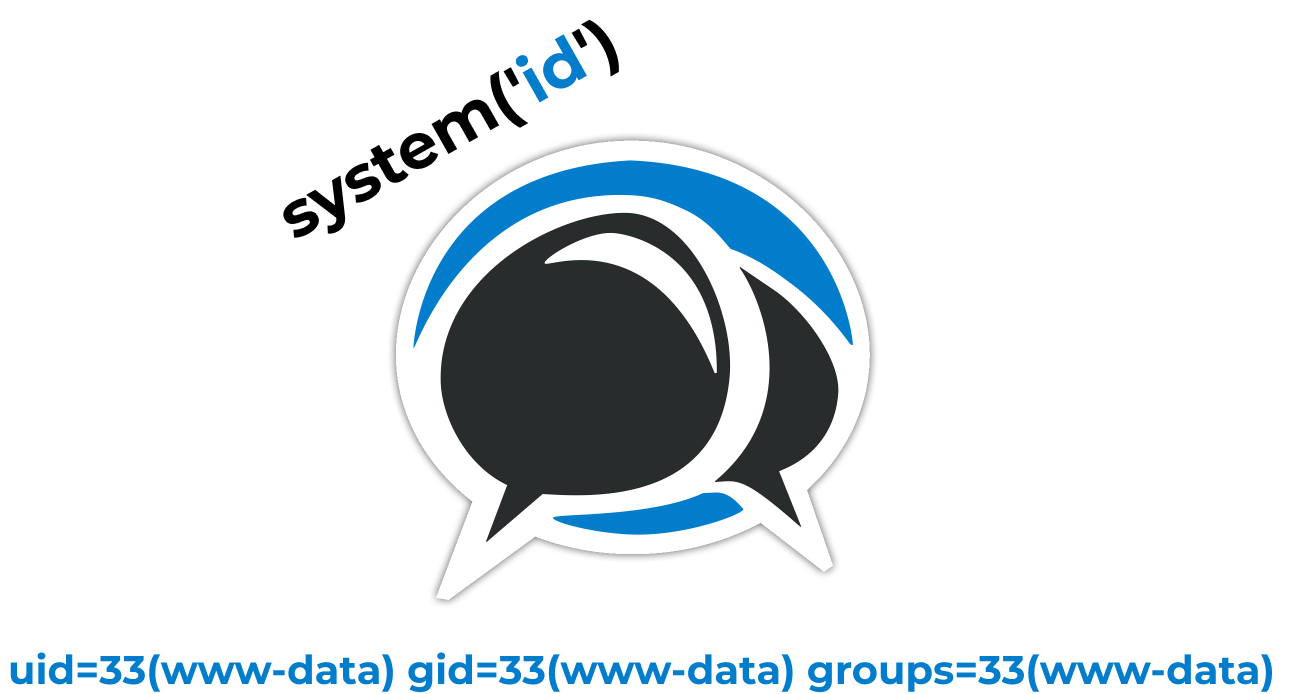
Continue readingMyBB <= 1.8.31: Remote Code Execution Chain
MyBB is one seriously popular type of open-source forum software. However, even a popular tool can contain bugs or even bug chains that can lead to the compromise of an entire system. In this article, we’ll go over one such chain that we found.
Continue reading